Albanian businesses face a phishing attack rate of 4.8% for organizations, with over 1,150 recorded incidents and an average breach cost of $1.2 million. High-profile cases like the SPAK email compromise showed that even institutions with resources can fall victim. For small and medium-sized businesses in Tirana, Durrës, and beyond, the stakes are just as high but the security budgets are far smaller. This guide gives you a practical, step-by-step email security workflow built for the Albanian SMB reality: limited IT staff, real local threats, and the urgent need to protect your communications starting today.
Table of Contents
- Recognize the risks: Why email security matters for Albanian SMBs
- Prepare your defenses: Essential tools and policies
- Step-by-step: Deploying your email security workflow
- Verify, monitor, and adapt: Ongoing security actions
- What most SMBs miss: The human factor in Albanian email security
- Upgrade your email security with Albanian experts
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Phishing risk is high | Albanian SMBs face significant phishing threats and costly breaches. |
| Tools and training matter | Combining technical controls with regular staff training strengthens defenses. |
| Workflow is ongoing | Effective email security requires continual monitoring, testing, and adaptation. |
| Local support helps | Partnering with experts familiar with Albanian challenges ensures better results. |
Recognize the risks: Why email security matters for Albanian SMBs
Email remains the number one entry point for cyberattacks against businesses worldwide, and Albania is no exception. The phishing rate of 4.8% for Albanian organizations, combined with 1,150 or more recorded incidents and an average breach cost of $1.2 million, paints a clear picture: this is not a theoretical problem. It is happening right now, to businesses like yours.
SMBs are particularly attractive targets. Attackers know that smaller organizations rarely have a dedicated security team, often run outdated software, and rely heavily on email for daily operations. The SPAK email incident was a wake-up call for many Albanian businesses. It demonstrated that spoofed or compromised emails can damage reputations, expose sensitive data, and trigger legal consequences, all at once.
"A single phishing email that tricks one employee can cost your business more than a year of proper security investment." This is not an exaggeration when you factor in downtime, data recovery, and lost client trust.
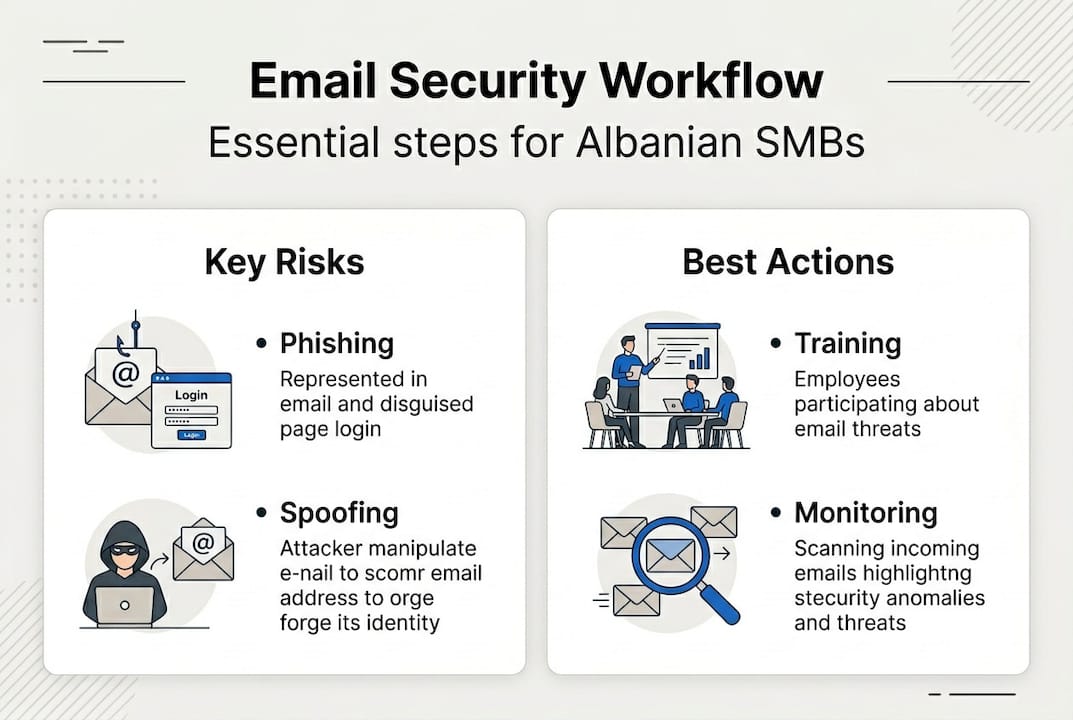
The most common attack vectors targeting Albanian SMBs include:
- Phishing emails that impersonate trusted senders like banks, government agencies, or partners
- Email spoofing where attackers forge the sender address to look legitimate
- Compromised credentials obtained through fake login pages or data leaks
- Business email compromise (BEC) where attackers impersonate executives to authorize fraudulent transfers
- Malicious attachments disguised as invoices or contracts
| Attack type | How it works | Typical damage |
|---|---|---|
| Phishing | Fake email tricks user into clicking | Credential theft, malware |
| Spoofing | Forged sender address | Brand damage, fraud |
| BEC | Impersonates executive | Financial loss |
| Malicious attachment | Hidden malware in file | Data loss, ransomware |
The reputational damage from a breach often outlasts the financial cost. Clients lose confidence, contracts get canceled, and rebuilding trust takes months. Reviewing regional breach examples can help you understand the real-world impact on businesses similar to yours. With the scale of these threats in mind, the next step is preparing your organization.
Prepare your defenses: Essential tools and policies
Before you can execute a security workflow, you need the right foundation. That means both technical tools and human policies working together. Skipping either one leaves a gap that attackers will find.
On the technical side, every Albanian SMB should implement these core email authentication standards:
- SPF (Sender Policy Framework): A DNS record that specifies which mail servers are allowed to send email on behalf of your domain
- DKIM (DomainKeys Identified Mail): Adds a digital signature to outgoing emails so recipients can verify they were not tampered with
- DMARC (Domain-based Message Authentication, Reporting, and Conformance): Ties SPF and DKIM together and tells receiving servers what to do with emails that fail authentication
- MFA (Multi-Factor Authentication): Requires a second verification step beyond a password, blocking most credential-based attacks
- Secure email gateway: Filters incoming and outgoing mail for spam, malware, and phishing before it reaches your inbox
Given the rising phishing rates and local incidents like the SPAK email case, aligning with these global best practices is not optional. It is the baseline.
| Tool | Key function | Estimated monthly cost |
|---|---|---|
| Google Workspace | SPF, DKIM, DMARC, MFA built-in | $6 to $18 per user |
| Microsoft 365 Business | Full email security suite | $6 to $22 per user |
| Proofpoint Essentials | Advanced threat filtering | $2 to $8 per user |
| Mimecast | Gateway, archiving, training | $3 to $10 per user |
Beyond tools, your staff needs a clear email usage policy. This should cover how to recognize suspicious emails, what to do when they receive one, and who to report it to. A written policy also sets expectations and gives you a basis for accountability. Reviewing your privacy policy updates alongside your email policy ensures both are aligned.

Pro Tip: Invest in employee training before you invest in premium tools. Most breaches start with a user clicking a link or opening an attachment. A well-trained team stops attacks that no software can catch.
Once your prerequisites are in place, you can roll out each step of the workflow.
Step-by-step: Deploying your email security workflow
With your tools and policies ready, here is the ordered workflow to implement email security across your business.
- Enable SPF on your domain. Log into your DNS provider and add a TXT record that lists your authorized mail servers. This takes under 30 minutes and immediately reduces spoofing risk.
- Set up DKIM. Generate a DKIM key pair through your email provider and publish the public key as a DNS TXT record. Your email provider's documentation will walk you through the exact steps.
- Configure DMARC. Start with a policy of "none" to monitor without blocking, then move to "quarantine" and finally "reject" as you confirm legitimate email flows are unaffected.
- Enforce MFA on all email accounts. Require every employee to set up MFA through your email platform. This single step blocks over 99% of automated credential attacks.
- Train your staff. Run a phishing simulation to establish a baseline, then deliver focused training on what to look for. Repeat this quarterly.
- Set up monitoring and alerts. Configure your email platform to alert you on suspicious login attempts, unusual forwarding rules, or failed DMARC checks.
- Define an incident response procedure. Document exactly what happens when a breach is suspected: who gets notified, what gets isolated, and how you communicate with affected parties.
With 4.8% of Albanian organizations experiencing phishing attacks, having a tested incident response plan is not a luxury. It is a requirement. You can also find practical IT security tips to supplement each step of this workflow.
Pro Tip: Automate your recurring security checks. Set calendar reminders for monthly DMARC report reviews and quarterly phishing simulations. Automation removes the risk of these critical tasks being skipped during busy periods.
Even with the best workflow, pitfalls can occur. Let's cover how to troubleshoot and avoid common mistakes.
Verify, monitor, and adapt: Ongoing security actions
Deploying your workflow is not the finish line. Ongoing verification is what keeps it effective as threats evolve.
Start with these verification steps:
- Use a free tool like MXToolbox to check that your SPF, DKIM, and DMARC records are correctly published and active
- Review your DMARC aggregate reports weekly during the first month, then monthly once stable
- Check email server logs for unusual patterns like high bounce rates or unexpected sending volumes
- Collect user feedback through a simple monthly survey asking staff if they noticed anything suspicious
- Run a follow-up phishing simulation every quarter to measure whether training is working
Common mistakes Albanian SMBs make after initial setup include:
- Setting DMARC to "none" and never moving to enforcement mode
- Forgetting to update SPF records when adding a new email service or marketing tool
- Skipping MFA for executives because they find it inconvenient
- Assuming a one-time training session is sufficient
- Not having a documented incident response plan before an attack happens
"Security is not a project you finish. It is a practice you maintain. Limited SMB resources make this harder, but they also make it more important to be consistent rather than reactive."
Set a monitoring schedule that works for your team size. A small business with two IT staff can still maintain strong security with a structured monthly review: check records, review logs, confirm MFA is active for all accounts, and document any anomalies. When you need additional support, expert support from a local provider can fill the gaps your internal team cannot cover. Maintaining your workflow is critical, but what separates good from great email security? Our perspective as local experts can help.
What most SMBs miss: The human factor in Albanian email security
After working with businesses across Tirana and Durrës, we have seen a consistent pattern: companies spend thousands on security tools and then lose data because one employee clicked a fake invoice link. Technology is necessary, but it is not sufficient.
The uncomfortable truth is that most breaches succeed because of gaps in user behavior, not gaps in software. Attackers do not need to bypass your firewall if they can convince your accounts manager to wire money to a fraudulent account. No tool stops that.
What works is building a security-first culture. That means short, practical training sessions every quarter, not a single annual presentation. It means making it easy and safe for employees to report suspicious emails without fear of embarrassment. It means leadership visibly following the same security rules as everyone else.
We have seen real-world case studies where a simple change in staff behavior, like pausing before clicking any link in an unexpected email, prevented what could have been a catastrophic breach. Expensive passive tools cannot replicate that vigilance. Invest in your people as seriously as you invest in your software.
Upgrade your email security with Albanian experts
Building and maintaining a strong email security workflow requires consistent effort, and most SMBs in Albania simply do not have the internal bandwidth to do it alone. That is where local expertise makes a real difference.

At Blad IT Solutions, we understand the specific threat landscape facing businesses in Tirana and Durrës. We offer expert IT services that cover everything from initial email security setup to ongoing monitoring, staff training coordination, and emergency incident response. Our team is available around the clock, so you are never left exposed when something goes wrong. Ready to take the next step? Book a consultation and let us help you build an email security workflow that actually holds up.
Frequently asked questions
What is the first step in an email security workflow for Albanian SMBs?
Start by assessing your current risks, including checking for phishing vulnerabilities and gaps in staff training. With a phishing rate of 4.8% and over 1,150 incidents recorded in Albania, knowing your exposure is the foundation of any effective response.
Why are SPF, DKIM, and DMARC important for email security?
They authenticate your outgoing emails and reduce the risk of spoofing and phishing attacks. Given the rising phishing rates in Albania, these three records form the non-negotiable baseline of any business email setup.
How often should I review my email security policies?
Review email security policies at least quarterly or after any incident to ensure they are current. Threats evolve quickly, and a policy written 18 months ago may not address the attack methods being used today.
What common mistakes should Albanian SMBs avoid in email security?
Avoid relying solely on technology. Most breaches succeed because of gaps in user behavior, not technology, so failing to train staff and update security policies regularly is the biggest risk most businesses overlook.
